Förderjahr 2025 / Stipendium Call #20 / ProjektID: 7761 / Projekt: Hidden Dangers: Uncovering Security and Privacy Risks through Large-scale Mobile App Analysis
Analyzing the iOS Local Network Permission from a Technical and User Perspective
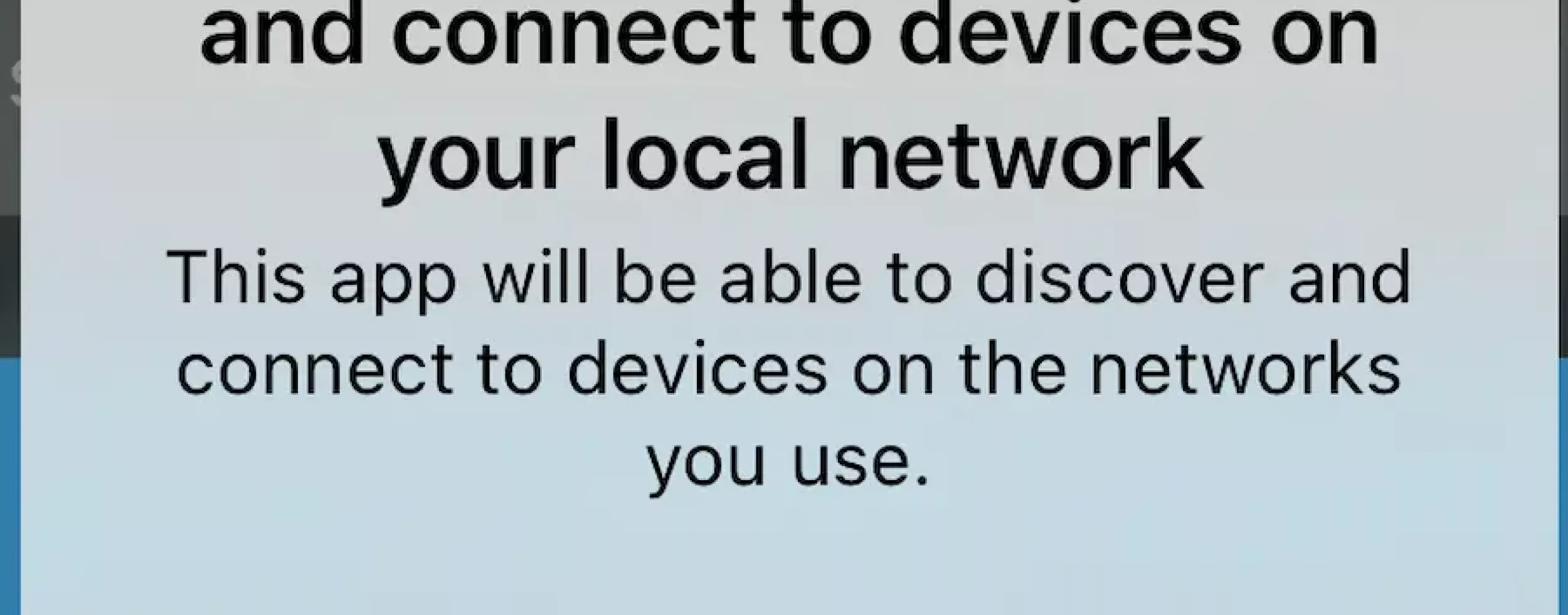
With the release of iOS 14, Apple introduced a dedicated permission to regulate apps' access to the local network. Although devices within local networks are typically shielded from direct Internet exposure, apps running on smartphones connected to such networks can communicate with other local devices. This capability opens a new attack vector and presents privacy risks, including tracking and household fingerprinting. Prior work showed that apps leveraged local network access to bypass the location permission, as the router's MAC address can reveal a user's location. Moreover, researchers identified malicious apps that attempted to attack routers via local network communication.
In this work, we systematically analyzed the iOS local network permission from both technical and user perspectives. The technical perspective is particularly relevant because this permission differs fundamentally from traditional permission models. Typically, permissions protect a set of operating system APIs. In contrast, the local network permission relies on runtime monitoring of network traffic destinations and prompts the user when the system detects access to local network resources. At the time of our study, Android did not yet provide a comparable permission, allowing us to investigate differences in their access behavior. From a user perspective, the intrinsic technical complexity of the permission raises the question of whether users can make informed decisions when confronted with the dialog.
We first evaluated the security of the permission's implementation by implementing a test app trying to access the local network through various methods. We then conducted a large-scale dynamic analysis to detect local network access in apps and compared the prevalence and characteristics of such access between Android and iOS apps. Next, we analyzed the developer-provided rationales for the permission. Finally, we conducted an online user study with 150 participants to assess users' understanding of the permission and its implications.
Our work revealed two methods to bypass the permission from webviews and showed that the protected local network addresses were insufficient. We found that 152 iOS apps and 117 Android apps accessed the local network, and that the timing of access differed: Android apps tended to access it at startup. Finally, we presented both the strengths and limitations of users' understanding of the permission. While nearly every participant was aware of at least one threat (83.11%), misconceptions were even more common (84.46%).
Link to the paper
The paper was presented at IEEE Security and Privacy 2025: https://www.computer.org/csdl/proceedings-article/sp/2025/223600a045/21…;


