Förderjahr 2017 / Science Call #1 / ProjektID: / Projekt: SEPSES
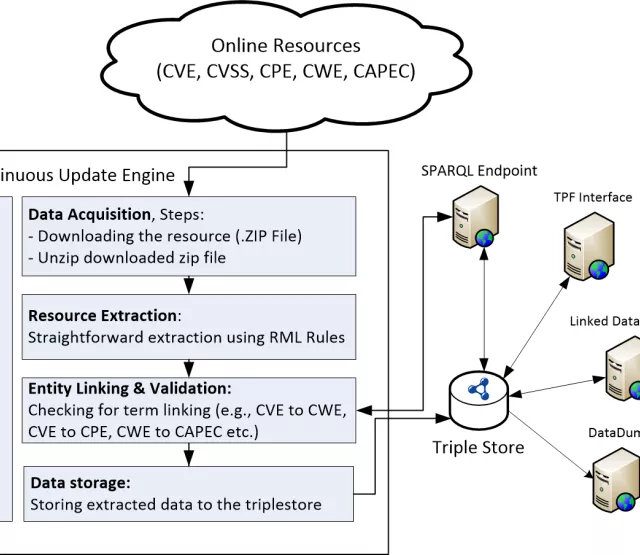
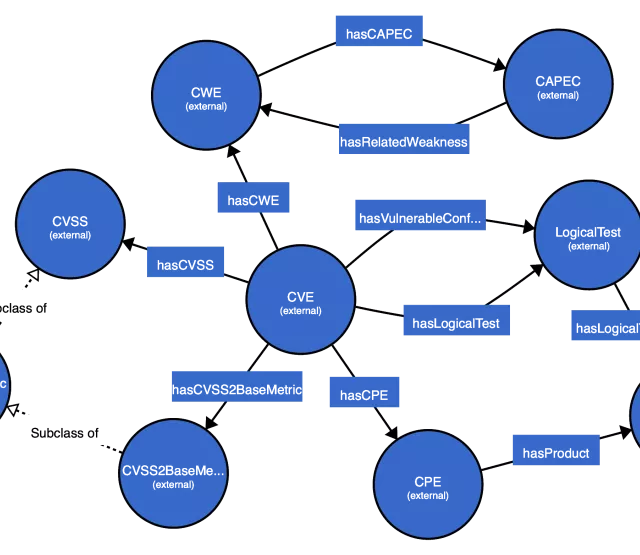
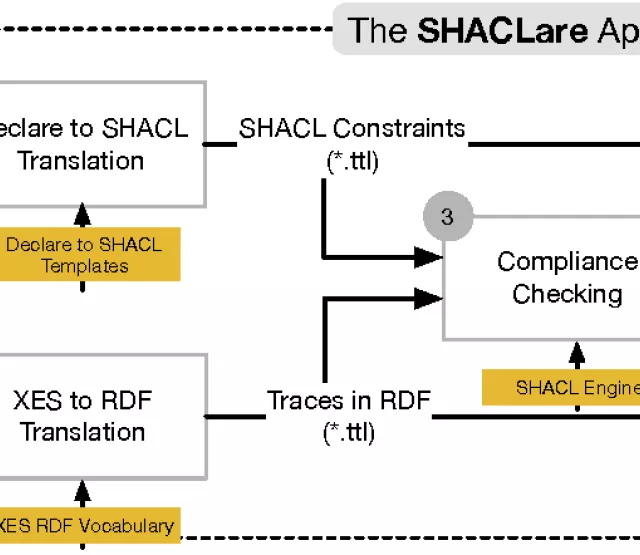
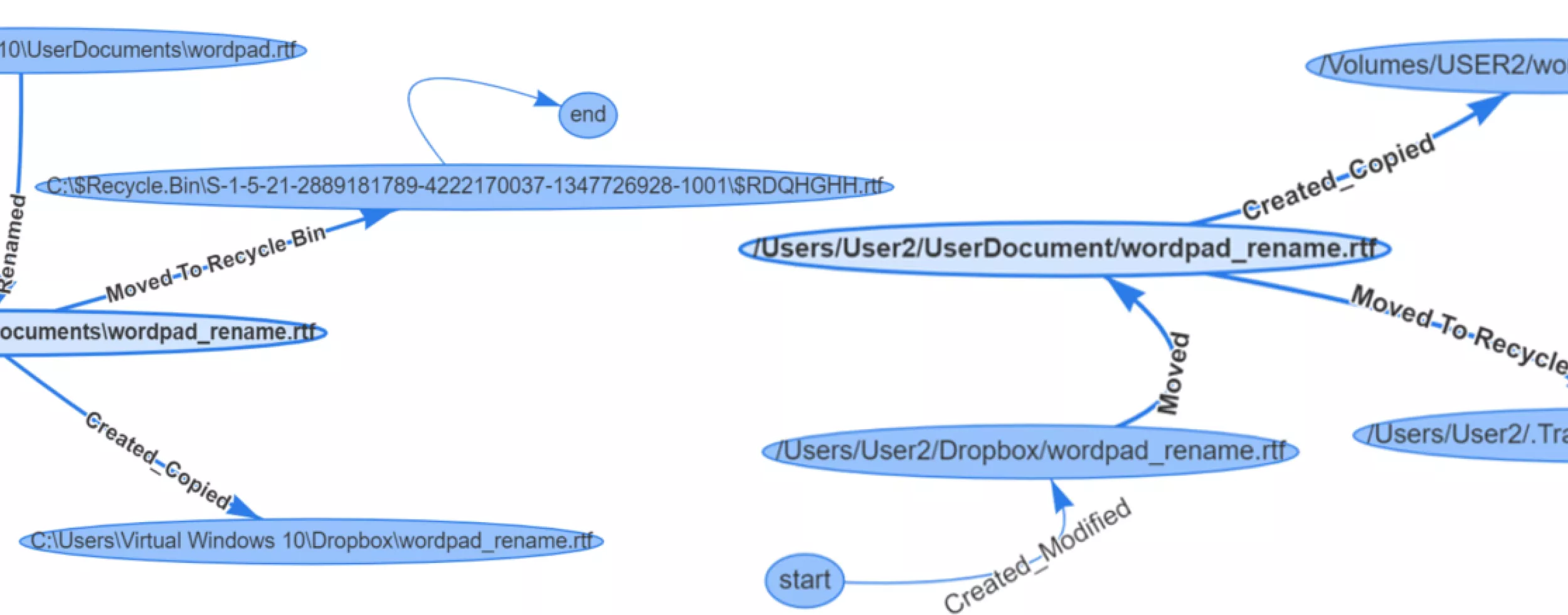
At the Semantics conference Poster & Demo Session in September in Karlsruhe, we will present our preliminary results on a semantic approach for monitoring file system activity. File access activity information is an important source for identifying unauthorized data transmissions. We tackle limitations of existing monitoring approaches in terms of semantic integration, contextualization, and cross-system interoperability. In particular, we defined a vocabulary for file activity logs and outline an architecture for log file collection, extraction, linking, and storage. We demonstrate the applicability of this approach by means of an application scenario. Finally, we show how analysts can inspect the life-cycle of files in a context-rich manner by means of SPARQL queries and a graph visualization of the results.
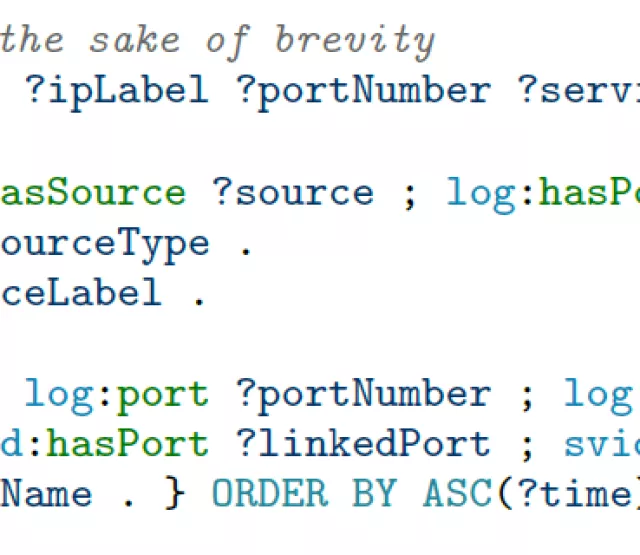
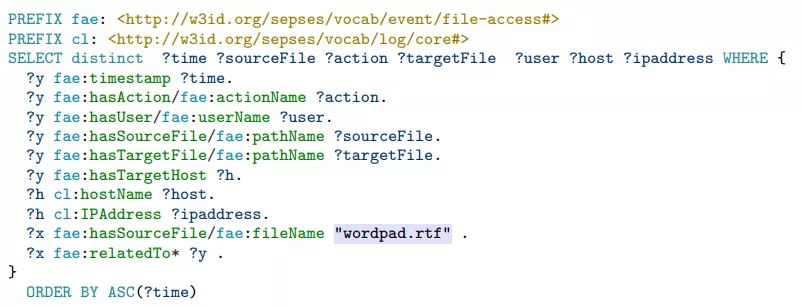
As an example, after collecting and integrating file events, a SPARQL query can be used to inspect the life-cycle of a specific file:
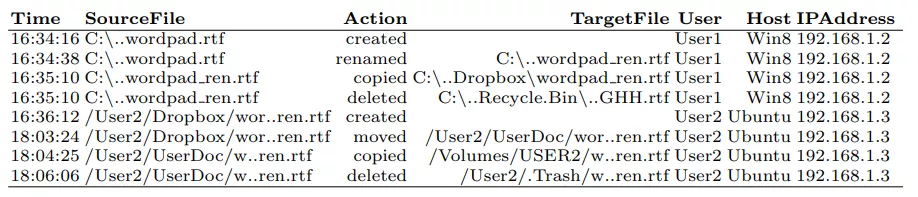
The result is illustrated in the table below:
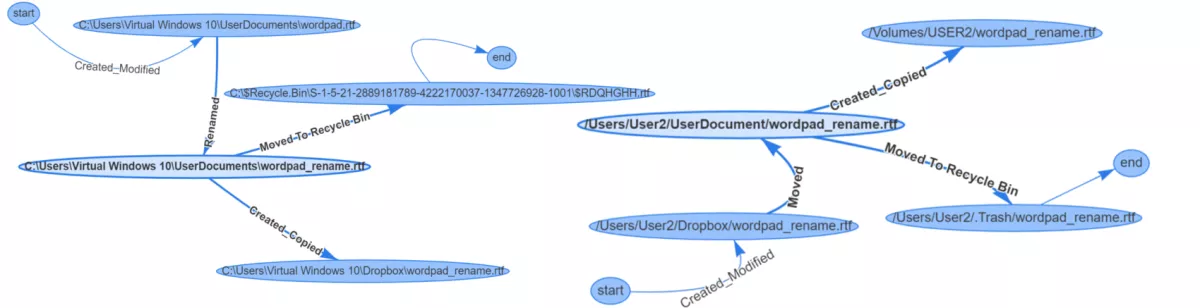
Finally, we can display the data in a graph representation:
Andreas Ekelhart